QEDO, QDP, Pyra Skills, frontend/backend separation
Quad_Dipped hashing security for Pyraclaw-sealed QEDO envelopes
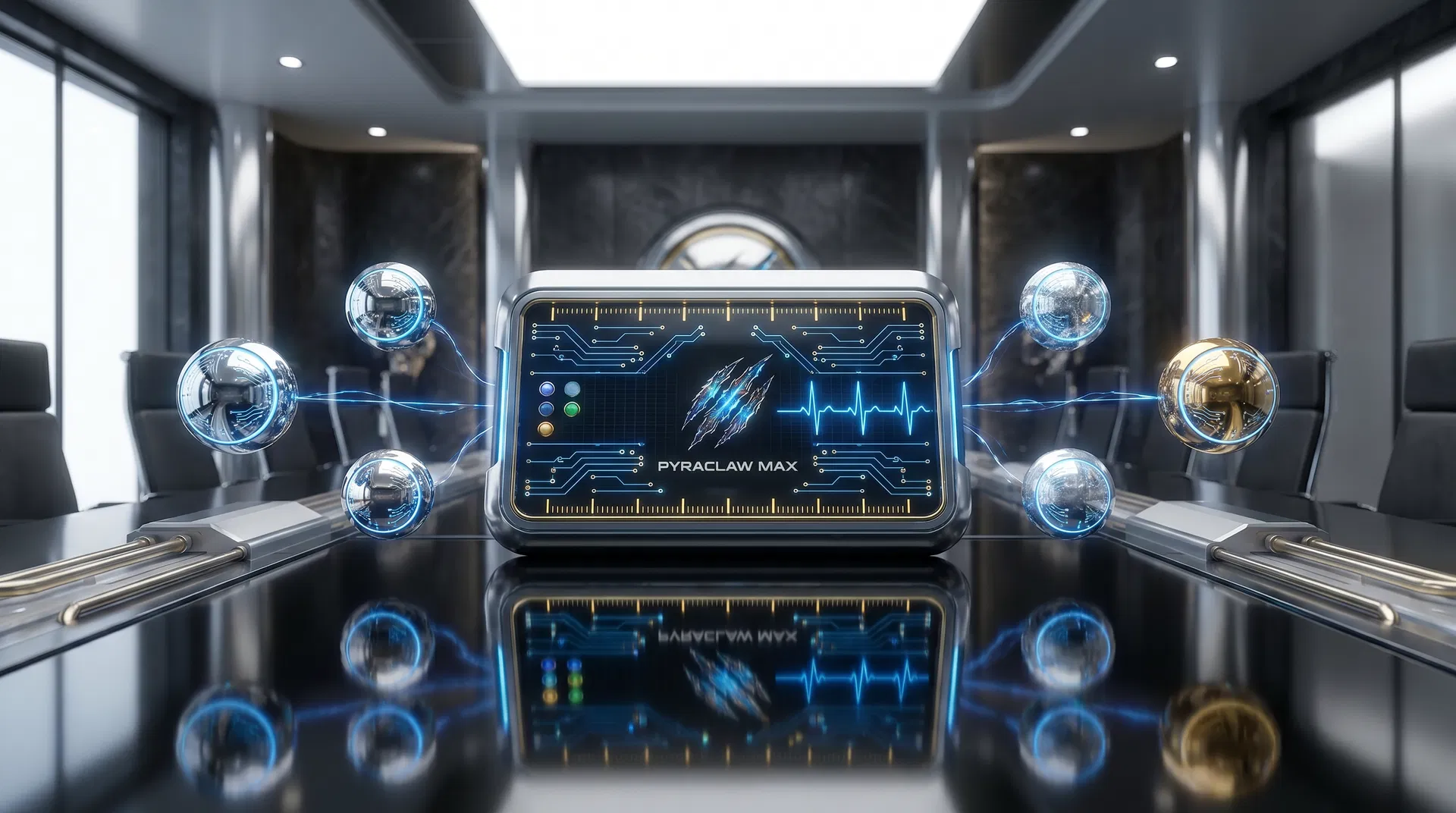
pyraclaw_max now speaks in a subtler boardroom language: mercury mirror, polished chrome, quicksilver, platinum, diamond silver, honeyed gold, and restrained electric-blue pulses. GitHub and Google Drive source value has been folded into a precise public interface that shows custody state, not private engines.
Quicksilver restraint, gold confirmation, and visible evidence geometry.
The refined platform commits fully to chrome, platinum, honey gold, diamond silver, mercury mirror, and electric-blue precision. GitHub contributed the QEDO, QDP, Pyra Skills, NVIDIA gateway, and frontend/backend separation discipline. Google Drive contributed the investor, EU readiness, licensing, and pilot-wedge language. The result is a high-definition interface that feels dynamic while staying honest: frontend motion is local, backend custody remains protected.
VC deck, EU briefing, pilot wedge, licensing posture
Motion rhythm, chrome/gold palette, voice and deck assets
One clean command plane for devices, orbs, benchmark nodes, and color-coded custody.
The schematic is designed for executive review: all major routes are visible, color-coded, and intentionally public-safe. It visualizes QEDO routing, QDP capsules, Cloudflare R2, NVIDIA/Brev, GuardianAngel review, and audit export without exposing live credentials, proprietary algorithms, or private hash layers.

Chrome orbs sized and color-coded for executive cognition.
Sphere size now communicates hierarchy, while color communicates custody state. Steel blue indicates runtime, electric blue indicates signal, honey gold indicates verified evidence, platinum white indicates oversight, and diamond silver indicates export readiness.


All attached files remain present inside one polished evidence wall.
The uploaded images, videos, PDF, and HTML pitch deck are all preserved in the platform. The two MP4 assets retain their embedded AAC audio through user-controlled playback, while the new mirror-metal assets establish the refined high-definition brand surface.
Technical Pitch Deck HTML
Original attached HTML deck retained as a downloadable source artefact.
Open assetTechnical Pitch Deck PDF
Investor material informing the forged, sealed, attested narrative.
Open asset



pClaw motion source
8.13s H.264/AAC media used for claw_ball rhythm and audio-capable motion.
Open asset
pClaw alternate motion
Second 8.13s H.264/AAC source integrated as a media pulse panel.
Open asset
22 brand-voice presets tuned for elegant, futuristic, evidence-first communication.
These voices are practical copy modes for decks, videos, web sections, narrators, and future audio generation. Each one preserves the same evidence-first ethic while giving Pyraclaw a wider tonal register.
pyra_voice_forge
Dense, metallic, decisive.
We do not release claims; we forge artefacts that can be defended.
pyra_voice_attestor
Precise, legal-aware, calm.
Every decision deserves provenance before it deserves distribution.
pyra_voice_guardian
Protective, risk-aware, restrained.
Candidate work remains held until the operator can prove why it should move.
pyra_voice_oracle
Visionary but bounded.
The next AI interface is not a chat box; it is a governed perimeter of proof.
pyra_voice_mercury
Fluid, reflective, adaptive.
The system moves quickly, but every reflection leaves a sealed trace.
pyra_voice_platinum
Premium, polished, investor-grade.
Pyraclaw Max turns orchestration into a defensible operating asset.
pyra_voice_diamond
Sharp, crystalline, high-clarity.
Logs can speak; capsules can testify.
pyra_voice_aegis
Shielding, sovereign, operator-first.
The operator owns the boundary; the evidence proves what crossed it.
pyra_voice_jellyfish
Ethereal blue, luminous, soft-power.
Blue light moves through the perimeter like a living seal.
pyra_voice_crown_gold
Warm, scarce, authoritative.
Gold is used sparingly, because certainty should never need excess.
pyra_voice_silverline
Linear, concise, technical.
Intercept. Reason. Gate. Seal. Anchor. Nothing leaves unaccounted.
pyra_voice_claw_ball
Rhythmic, kinetic, pulse-driven.
The sphere turns with the heartbeat of custody.
pyra_voice_three_rip
Logo-forward, memorable, compact.
Three ripples, one perimeter: forged, sealed, attested.
pyra_voice_qedo
Ontology-aware, methodical.
A task becomes credible only when its lineage, gate, and verdict are visible.
pyra_voice_rsfs
Review-focused and skeptical.
Promotion is not assumed; it is reviewed, reflected, and justified.
pyra_voice_investor_gate
Commercial, concise, evidence-led.
The category belongs to teams that can prove their AI operations before procurement asks.
pyra_voice_cloudflare_bridge
Infrastructure-literate, redacted.
The gateway belongs behind the wall; the interface shows only the custody state.
pyra_voice_nvidia_brev
Compute-aware, performance-minded.
Acceleration matters only when custody survives the speed.
pyra_voice_hamburg_anchor
Jurisdictionally grounded.
The operating posture is European by default: measured, evidenced, and defensible.
pyra_voice_quicksilver
Fast, bright, premium technical.
Swift motion, mirrored proof.
pyra_voice_honey_gold
Warm, humane, humble.
The technology is advanced; the promise remains simple: help operators prove their work.
pyra_voice_sovereign_chrome
Grand, polished, but controlled.
A sovereign AI perimeter should feel powerful because it is accountable.

Cloudflare, NVIDIA/Brev, and Manus API merge as one guarded backend posture.
The platform can acknowledge your Cloudflare R2 bucket family and Worker gateway concept, but the frontend is intentionally redacted. Environment variables such as PYRA_CF_GATEWAY_URL and PYRA_SHARED_SECRET are implementation notes for a secure backend or Worker, never public client code.
Cloudflare R2
Redacted evidence-media storage
Public UI may show bucket family and custody posture, never write credentials.Worker gateway
/v1/pyra/infer behind shared-secret auth
Worker secrets remain server-side; static pages cannot hold PYRA_SHARED_SECRET.NVIDIA API + Brev
GPU-backed guarded inference option
Acceleration belongs behind backend routes or controlled compute custody.Manus API
Agentic task automation and structured-output workflows
API keys must live in secure backend or project secret storage only.pyraclaw_max
Manual-first QEDO envelope adapter
HTTP mode is disabled until endpoint and operator approval are explicitly configured.Five stages, visible enough for trust, sealed enough for security.
Intercept
Every prompt, retrieval, and tool call enters the operator boundary before touching a model.
Reason
Candidate work runs inside a bounded context with lineage and stage-gate vocabulary preserved.
Gate
Guardian / RSFS review language holds promotion until evidence can justify the movement.
Seal
Visible UI exposes capsule IDs and public states while private QDP details remain backend-only.
Anchor
The brand promise remains: build forged, attest everything, overclaim nothing.
Build a frontend-safe QEDO envelope without leaking the seal.
Select a system line, mode, and stage gate. The interface exposes only the public candidate state, capsule ID, and manual-prompt contract. Actual QDP hash layers, shared secrets, worker credentials, Manus API keys, NVIDIA tokens, and Brev access stay behind the operator boundary.
Foundation bond
Operator-grounded candidate tasks, manual custody, and p_33 substrate-stage semantics tied back to the original 32 pyra_structure foundation.
Low autonomy: ideal for first sealed envelope demonstrations.EVC-P33-POC-MANUAL-DEMOMANUALPOCHOLD{
"schema": "dd7.pyraclaw.max_task/v1",
"adapter": {
"name": "pyraclaw_max",
"version": "0.1.0",
"target": "MiniMax Agent surface"
},
"qedo": {
"system_line": "p_33",
"stage_gate": "POC",
"verdict_status": "candidate-pending-human-review",
"requires_rsfs_review": true,
"requires_backend_evidence_seal": true
},
"task": {
"task_id": "max-demo-p_33-poc",
"objective": "Prepare a QEDO-ready NVIDIA/Brev/Manus bridge task for MiniMax Agent while preserving RSFS review, p_33 lineage, Cloudflare-gateway secrecy, and backend-only evidence sealing.",
"system_line": "p_33",
"operator": "pyraclaw",
"context": {
"demo_surface": "pyraclaw_max mirror-metal bridge platform",
"runtime_visibility": "frontend-safe-summary-only",
"cloudflare_r2": "configured-backend-only-redacted",
"nvidia_brev": "compute-intent-not-client-call",
"source_value": "github-and-google-drive-extracted-into-public-safe-copy"
},
"constraints": {
"external_submission": "disabled",
"unsupported_claims": "blocked",
"secrets": "never embed Cloudflare, NVIDIA, Brev, Manus, or gateway secrets in frontend code",
"guardian_verdict_capsule": "not_required_for_demo"
},
"stage_gate": "POC",
"verdict_status": "candidate-pending-human-review"
},
"mode": "manual",
"delivered": false,
"evidence": {
"capsule_id": "EVC-P33-POC-MANUAL-DEMO",
"qdp_status": "sealed-backend-only",
"rsfs_gate_result": "HOLD",
"visible_detail": "capsule-id-and-status-only"
}
}Do not publish secrets in the static interface.
The Cloudflare Worker URL, R2 endpoint family, and variable names can be documented, but live secrets and write credentials must be injected only in backend/Worker runtime configuration. This static site deliberately avoids calling those services directly.
Manual mode remains the reliable default.
The demo supports operator-reviewed envelopes today. HTTP and connector flows remain guarded because they require explicit backend configuration, secret custody, and action approval.
Deep solutions. Sharp minds. Sovereign technology.
Pyraclaw Max now speaks in quicksilver, chrome, platinum, gold, and electric-blue proof: cinematic enough to be remembered, restrained enough to be trusted, and engineered around the promise that every meaningful output should be sealed before it is celebrated.